
De-identification and re-identification of PII in large-scale datasets using Cloud DLP | Cloud Architecture Center | Google Cloud
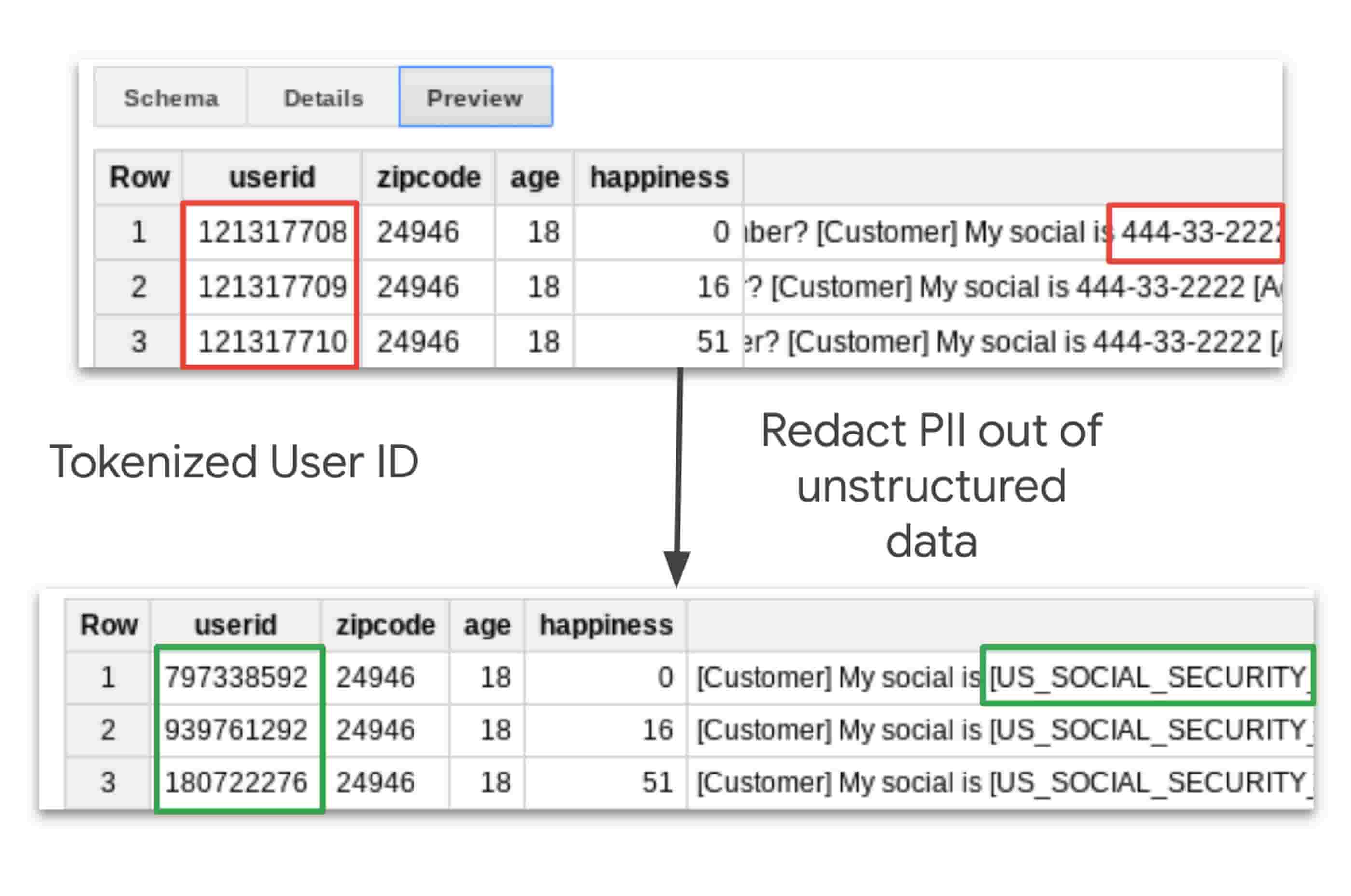
Taking charge of your data: using Cloud DLP to de-identify and obfuscate sensitive information | Google Cloud Blog
Data Masking Counter Attack to Identity Theft Paul Preston Data Masking: Counter Attack to Identity Theft. - ppt download

Primer on GDPR Pseudonymization. Personal data is any information… | by Balaji Ramakrishnan | Medium
Data Obfuscation Vs Data Masking Ppt Powerpoint Presentation Infographics Outline Cpb | PowerPoint Templates Backgrounds | Template PPT Graphics | Presentation Themes Templates




![Data Masking and Encryption Are Different [video] - IRI Data Masking and Encryption Are Different [video] - IRI](https://i.ytimg.com/vi/LuO7bi9uRh4/maxresdefault.jpg)







![1. Introduction - Anonymizing Health Data [Book] 1. Introduction - Anonymizing Health Data [Book]](https://www.oreilly.com/library/view/anonymizing-health-data/9781449363062/images/anhd_0101.png)
